What you need to know about the Protection of Critical Infrastructures (Computer Systems) Ordinance, the cybersecurity legislation in Hong Kong (Part 1)
The Protection of Critical Infrastructures (Computer Systems) Ordinance (Cap. 653) came into force in Hong Kong on 1 January 2026. This is the first substantial horizontal cybersecurity legislation in Hong Kong. We will explore the scope and impact of this legislation in a series of articles, focusing in a Q&A format on the key issues businesses and industries need to be aware of.
In this first article, Pádraig Walsh from our Cybersecurity practice reviews who qualifies as critical infrastructure operators, how operators are designated, and which sectors fall under the regulatory ambit of the Commissioner of Critical Infrastructure (Computer-system Security) and sector regulators.
Introduction
1.1 Is there a cybersecurity law in Hong Kong?
Yes. The Protection of Critical Infrastructures (Computer Systems) Ordinance, (Chapter 653, Laws of Hong Kong) (“PCICSO”) came into operation on 1 January 2026. This is a comprehensive cybersecurity law, focussing on the protection of critical computer systems in critical infrastructure from cybersecurity risk.
1.2 What is the competent regulatory authority?
The Office of the Commissioner of Critical Infrastructure (Computer-system Security) (“CICS Commissioner”) is the competent regulatory authority. This office is a division of the Security Bureau of the Government of Hong Kong, and is not an independent statutory body.
1.3 What is the role of designated regulatory authorities?
Some regulatory responsibilities are shared with designated statutory sector regulators. Specifically, PCICSO designated the Monetary Authority and the Communications Authority (“Designated Regulators”) as competent regulators to directly supervise the responsibilities for organisational and preventive obligations under PCICSO in respect of certain regulated entities under its regulatory purview, as summarised below:
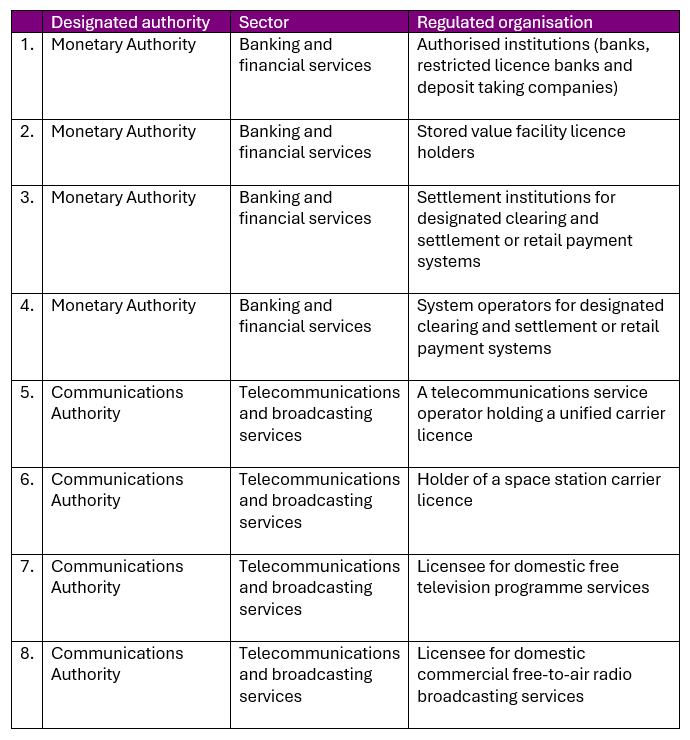
This reflects that the Monetary Authority and Communications Authority already regulate their respective sectors with a degree of sophistication and familiarity with the operations and needs of the relevant sectors. This will avoid duplication of effort with the remit of the CICS Commissioner.
The means that the Monetary Authority and Communications Authority, as designated authorities under PCICSO, will perform these functions in respect of CI Operators under their scope of authority:
(a) Identify and designate CI Operators and critical computer systems;
(b) Monitor CI Operators’ compliance with organisational and preventive obligations under PCICSO;
(c) Issue codes of practice to CI Operators, setting out the proposed standards for the organisational and preventive obligations. This can include adopting Codes of Practice published by the CICS Commissioner, as well as supplementing with sector specific Codes of Practice; and
(d) Issuing a written direction to a CI Operator if it has failed to fully comply with organisational or preventive obligations under PCICSO.
The CICS Commissioner will be responsible for regulating CI Operators of all sectors (including banking and financial services and telecommunications and broadcasting services) for incident reporting and response obligations.
1.4 How will the regulation be applied?
The main piece of legislation is the PCICSO. The CICS Commissioner will issue codes of conduct, guidelines and forms. The CICS Commissioner issued a General Code of Practice on 1 January 2026 [link], and a Code of Practice for the Energy Sector on 28 January 2026 [link]. We can expect the CICS Commissioner to publish other sector-specific Codes of Practice.
Codes of Practice are not subsidiary legislation. Failure to comply with the requirements of a Code of Practice would not in itself constitute an offence. However, the CICS Commissioner may issue written directions to require a CI Operator to take appropriate actions in relation to compliance with obligations under the PCICSO. Those directions are likely to be based on requirements set out in Codes of Practice, and compliance will be measured against the relevant provisions in the Code of Practice. Failure to comply with directions issued by the CICS Commissioner is an offence.
Guidelines are non-binding.
The Regulatory Perimeter
2.1 Who and what is the target of regulation under PCICSO?
The primary target of regulation is the protection of critical infrastructure and designated computer systems operated by designated critical infrastructure operators in Hong Kong. Direct regulation will only apply to large organisations. Only organisations designated by the authorities will be subject to PCICSO.
2.2 What is not regulated under PCICSO?
PCICSO does not cover, or is not intended to cover:
(a) Government departments. The Hong Kong Government already applies internal Government Information Technology Security Policy and Guidelines.
(b) Personal data, trade secrets and business information in computer systems. Personal data is already subject to regulation of the Office of Privacy Commissioner for Personal Data (“PCPD”) under the Personal Data (Privacy) Ordinance, Chapter 486, Laws of Hong Kong (“PDPO”).
(c) Small and medium size organisations or the general public.
2.3 What are critical infrastructure operators?
Critical infrastructure operators (“CI Operators”) are businesses or organisations that operate critical infrastructure. We analyse that description more in the paragraphs below.
2.4 What is critical infrastructure?
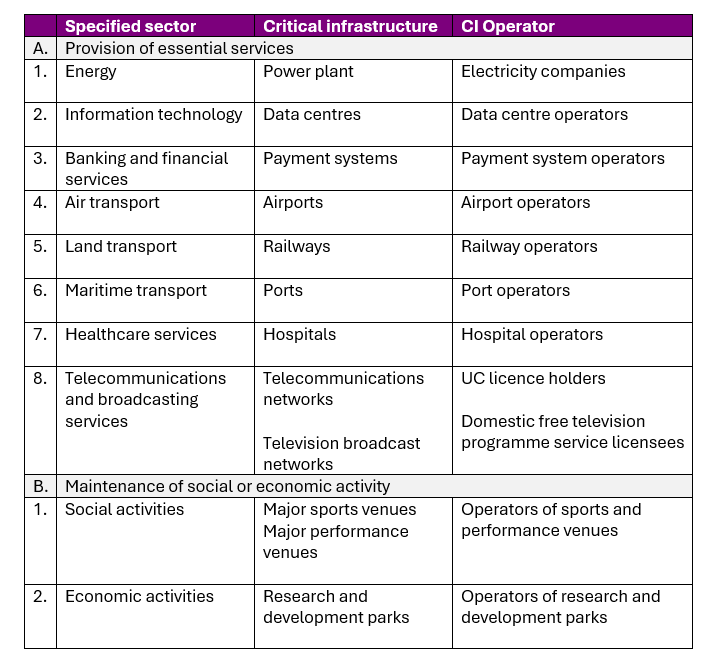
Critical infrastructure is any infrastructure that is essential to the continuous provision in Hong Kong of an essential service in a specified sector, and any other infrastructure the damage, loss of functionality or data leakage of which may hinder or substantially affect the maintenance of critical societal or economic activities in Hong Kong.
2.5 What are the specified sectors of CI Operators?
The specified sectors are:
- Energy
- Information technology
- Banking and financial services
- Air transport
- Land transport
- Maritime transport
- Healthcare services
- Telecommunications and broadcasting services
2.6 What are examples of critical infrastructure and CI Operators?
2.7 What does designation mean?
Not all businesses in the specified sectors are directly subject to the obligations of PCICSO and the regulatory oversight of the CICS Commissioner or the Direct Regulators under PCICSO. Direct regulation will only apply to large organisations, and will not apply to small and medium size organisations or the general public.
Designation is the process the CICS Commissioner and Designated Regulators will use to identify CI Operators, and the designated computer systems, that will be subject to direct regulation. The process will involve the CICS Commissioner and Designated Regulators identifying critical infrastructure, the CI Operators operating the critical infrastructure, and the critical computer systems relied upon in those operations.
The CICS Commissioner and the Designated Regulators have the statutory power to require operators to provide information he reasonably believes necessary to ascertain and assess each level of enquiry, from assessment of critical infrastructure, assessment of operators and ultimately, assessment of computer systems. It is an offence for an operator to fail to comply with an information request of the CICS Commissioner or Designated Regulators.
2.8 How will critical infrastructure be identified?
In general, the CICS Commissioner and Designated Regulator will have regard to:
(a) the kind of service provided by the infrastructure.
(b) whether there would be disruption or other significant impact to critical societal or economic activities in Hong Kong if the infrastructure was damaged, lost functionality or suffered data leakage.
2.9 What factors will be applied in the designation of CI Operators?
The factors considered when designating an organisation as CI Operator include:
(a) The extent of dependence of core functions on computer systems;
(b) The sensitivity of the data controlled by the infrastructure concerned; and
(c) The extent of control over the operation and management of the infrastructure concerned by the CI Operator in Hong Kong.
2.10 What factors are considered in the designation of critical computer systems?
The ultimate target of PCICSO and the primary concern of the CICS Commissioner and Designated Regulators is the protection of critical computer systems (“CCS”) in the operation of critical infrastructure by CI Operators.
These factors must be taken into account before designating a computer system as a CCS:
(a) the role of the computer system in core functions of the critical infrastructure;
(b) the impact of disruption or destruction of the computer system on core functions;
(c) the extent to which the computer system is related to other computer systems of the CI Operator;
(d) the extent to which the computer system and other computer systems of the CI Operator are related to those of other CI Operators and the computer systems other CI Operators use;
(e) the sensitivity of digital data stored or processed by the computer system that are used directly in the provision of essential services; and
(f) any information provided by the CI Operator.
Operational technology systems can also be considered as computer systems for the purpose of PCICSO. These systems could include supervisory control and data acquisition systems, distributed control systems or programmable logic controllers.
Underlying IT infrastructure of a computer system could also be regarded as components of the computer system, and within the scope of regulation under PCICSO. This could include network components, operating platforms, middleware, IoT devices and uninterruptible power supply systems.
2.11 What information is required to assess designation?
The CICS Commissioner and the Designated Regulators have discretion to require an operator to provide information reasonably necessary for learning about the operator and its critical computer systems.
In practice, this is likely to include:
(a) organisation chart of the operator;
(b) system functions;
(c) network infrastructure diagram and architecture;
(d) nature and volume of data processed;
(e) manufacturers and models of hardware and software;
(f) third party IT or telecom services provided by third parties;
(g) backup plans;
(h) information and technical specifications of the system design and operation; and
(i) other facts and functions about the computer system, including upstream and downstream dependencies.
2.12 How will an operator know it has been designated for compliance with obligations under PCICSO?
The process of designation is initiated by the CICS Commissioner and Designated Regulator through communication. The decision to designate will be notified in writing by the CICS Commissioner or Designated Regulator, setting out the effective date and CCS covered.
2.13 Is designation of a CI Operator or CCS made public?
No.
The sectors included under the ambit of PCICSO are the conventional sectors in similar legislation in other jurisdictions. PCICSO though will follow a designation process. Simply being a significant business in a covered sector does not automatically make a business subject to the legislation. There will be a formal process of designation that will pragmatically and systematically brings organisations under the purview of the CICS Commissioner (or designated regulator) over time.
In the next article in this series, we will look at the organisational obligations and certain preventative obligations under PCICSO.
Padraig Walsh
If you want to know more about the content of this article, please contact:
Pádraig Walsh
Partner | Email
Disclaimer: This publication is general in nature and is not intended to constitute legal advice. You should seek professional advice before taking any action in relation to the matters dealt with in this publication. This article was last reviewed on 31 March 2026.
